The Sushant Singh Rajput case took a strange turn when news channels started displaying WhatsApp conversations of Bollywood actors. As the WhatsApp ‘leaks’ became a daily feature of prime time news, the shock of the message content disappeared and public began to wonder, ‘How are news channels getting access to this content? Isn’t WhatsApp conversation supposed to be encrypted?’
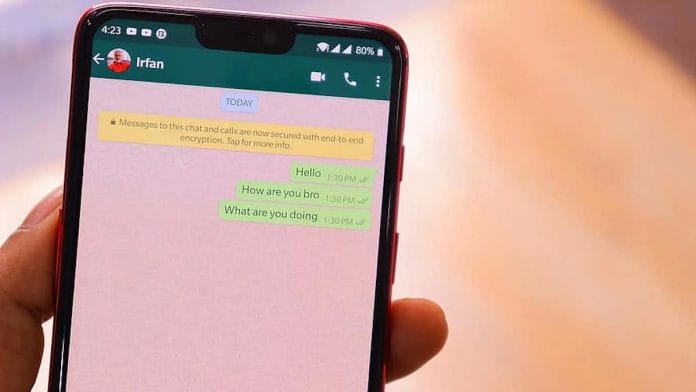
A natural, but erroneous conclusion, was that the messaging app was not as secure as it claimed to be. When starting a WhatsApp conversation, a yellow sticker on the top of the chat reminds the user that ‘Messages and calls are end-to-end encrypted. No one outside of this chat, not even WhatsApp, can read or listen to them’. The same line has been publicly repeated by WhatsApp in its response to law enforcement authorities (LEAs) who have requested data on WhatsApp users. With journalists accessing message conversations, it was natural to wonder if the platform was disingenuous in its public claims and if it could, in fact, access personal conversations and share them with law enforcement or other entities.
The prospect of weak encryption and security on WhatsApp has serious implications for the safety of the over 40 crore users of the messaging app in India.
Also read: India & 6 countries want to see encrypted messages, but Facebook ‘will maintain’ user security
How WhatsApp messages are read
Journalistic reporting has documented the use of WhatsApp, and more specifically WhatsApp groups for campaigning and organising. WhatsApp’s utility and popularity, however, is supported by its use in mundane and bureaucratic conversations, many of which are sensitive. During Covid tests, patients were asked to send Aadhaar details to the laboratories on WhatsApp. Anecdotes suggest that government officials routinely use the app to share official documents with each other.
After multiple days of prime time news coverage of individuals’ private WhatsApp messages, the company put out a statement reiterating their aforementioned claim of the platform being end-to-end (E2E) encrypted. Security experts also moved to dispel the theory of WhatsApp’s involvement in the leaks. For those of us who had studied the app carefully, it was clear that WhatsApp messages could only have been retrieved by gaining control, even if for a short duration, of the person’s device. This control could be gained through spyware such as Pegasus, or through physical access to the device itself.
An analysis of the images of WhatsApp conversations showed on news channels revealed that, in this case, it was the latter. Someone had physically accessed the phones, possibly for a short duration, during which the device was cloned. Since people don’t willingly yield their phones to journalists, the most plausible explanation remains that law enforcement authorities accessed the celebrities’ phones during their interrogation – the messages were leaked to the media by someone involved in the investigation.
Also read: How to prevent Navika Kumar from reading your private WhatsApp chats
Security needs a better solution
This episode raised a number of questions regarding the legality of accessing private conversations, the admissibility of these messages as evidence in court and the ethics of journalism. It is also an illuminating addendum to the fast-evolving global debate on weakening encryption standards in service of crime prevention and national security.
Earlier this year, an ad hoc committee of the Rajya Sabha recommended that LEAs be allowed to break E2E encryption on platforms such as WhatsApp to trace distributors of child pornography. A recent document leaked out of the European Union suggests that the EU might be similarly motivated to remove strong end-to-end encryption. The Australian government, leading the charge, passed a law in 2018 that creates “frameworks for…mandatory industry assistance to law enforcement”. This assistance could include removing encryption standards applied by communications platforms.
These laws and proposals are premised on the technical feasibility of a ‘backdoor’ to E2E communications that is accessible only by the government. Such a backdoor doesn’t exist. A backdoor for the government is also an entrance for ill-intentioned hackers. Furthermore, the WhatsApp leaks to media in the Sushant Singh Rajput case are a warning against uncritical faith in the integrity of LEAs to not misuse their surveillance powers.
Also read: How did leaked Bollywood ‘drug chats’ affect WhatsApp? Its downloads saw 25,000/day jump
The recent WhatsApp leaks in the Sushant Singh Rajput case and the Pegasus Spyware targeted at Indian citizens in 2019 show that LEAs possess technical tools and legal impunity to access encrypted communication, without needing a backdoor. The efficacy of extensive access to private communication for criminal investigations, especially related to child sexual abuse, is also unclear. Serious criminals are known to use specialised encrypted mobile phones. Backdoors to encrypted platforms used by everyday citizens might increase the visibility of petty online crime, but it won’t necessarily result in detection of terrorism or the power centres of criminal activity. It will, however, make millions of Indians more susceptible to scams and data breaches.
With media channels accessing an individual’s personal communication, it is clear that India needs a data protection law to safeguard its citizens from non-consensual access to their private communication. What is also clear is that Indian law enforcement already has the mechanism for targeted access to communication for crime prevention and detection. If the safety of citizens is the end objective, LEAs are better off with tools that work in conjunction with end-to-end encryption rather than those that undermine it.
Tarunima Prabhakar is a nonresident scholar at Carnegie India and project and research lead at Tattle Civic Tech.
This article is part of a series examining The Geopolitics of Technology in partnership with Carnegie India, leading up to its virtually held Global Technology Summit 2020 from 14-18 December 2020. More details about the summit are available here. ThePrint is a digital partner.
Read all the articles in the series here.





Don`t want to be hacked? Join Utopia, and stay cyber protected and anonymous!
Good
Use Signal App if you don’t want to ruin the open source.
Time to switch to Signal (Signalapp). Whatsapp is using Signal’s encryption protocol, but owned by FaceBook which is always will be trying to get into your communication