New Delhi: The Union Ministry of Electronics & Information Technology (MeitY) will Thursday relaunch an app that seeks to tip people off on possible interactions with coronavirus patients or carriers.
The app, ‘Corona Kavach’, was earlier taken off the Google Play store for further testing, MeitY spokesperson Rajeev Jain told ThePrint. It had been released just a few days earlier for beta testing, a final examination phase to get user feedback.
‘Corona Kavach’ has been developed by MeitY’s National e-Governance Division (NeGD) and uses your phone number, GPS, and the Indian Council of Medical Research (ICMR) database on patients who have tested positive for Covid-19. Through this information, the app seeks to alert users on whether they came in contact with any coronavirus patient.
Jain told ThePrint Wednesday that the app is “relaunching tomorrow… and will offer a better user experience”.
Corona Kavach is one of at least two app-based interventions from the government to keep people safe during the pandemic. The government thinktank Niti Aayog is also slated to launch an app, CoWin-20, which will not just track users but also offer information on testing centres and quarantine facilities.
Countries around the world are relying on tracking apps to keep a tab on active Covid-19 patients and carriers, and alert those they may have come in contact with. As Covid-19 is highly infectious, these apps are meant to check its spread and help break the chain of transmission.
Also Read: Zoom, the app designed by a Chinese immigrant now used by millions working from home
Corona Kavach features
The app initially released on Google Play store was only compatible with the android operating system and not iOS. ThePrint has sent a query in this respect via WhatsApp to the IT ministry spokesperson, and is awaiting a response.
Hyderabad-based security researcher Sai Krishna Kothapalli, founder of cybersecurity firm Hackrew, found Corona Kavach app on Google Play on 24 March, but tweeted on 29 March that it was no longer available.
@GoI_MeitY what happened to the Corona Kavach app on Play Store? I couldn't find it. Is it removed and why?
It was available a couple of days ago.
— Sai Krishna Kothapalli (@kmskrishna) March 28, 2020
However, Kothapalli was able to access the ‘Android Package Kit (APK)’ for the app. A file format specifically for android-based software, an APK contains all the code required to run a particular app. A user looking to test an app can simply download the APK on their phones before its official release.
The difference between downloading an app via an APK and accessing it through a store is that the latter is a trusted source and a user can be more assured that it is free of harmful software.
ThePrint downloaded the Corona Kavach app through its APK to give it a try.
As soon as the installation is completed, the app seeks your phone number and access to multiple things: Making and managing phone calls, photos and media, and device location.
It uses GPS data to “detect whether the device (you) came in the range of anyone who is either a host or a carrier of Covid-19”.
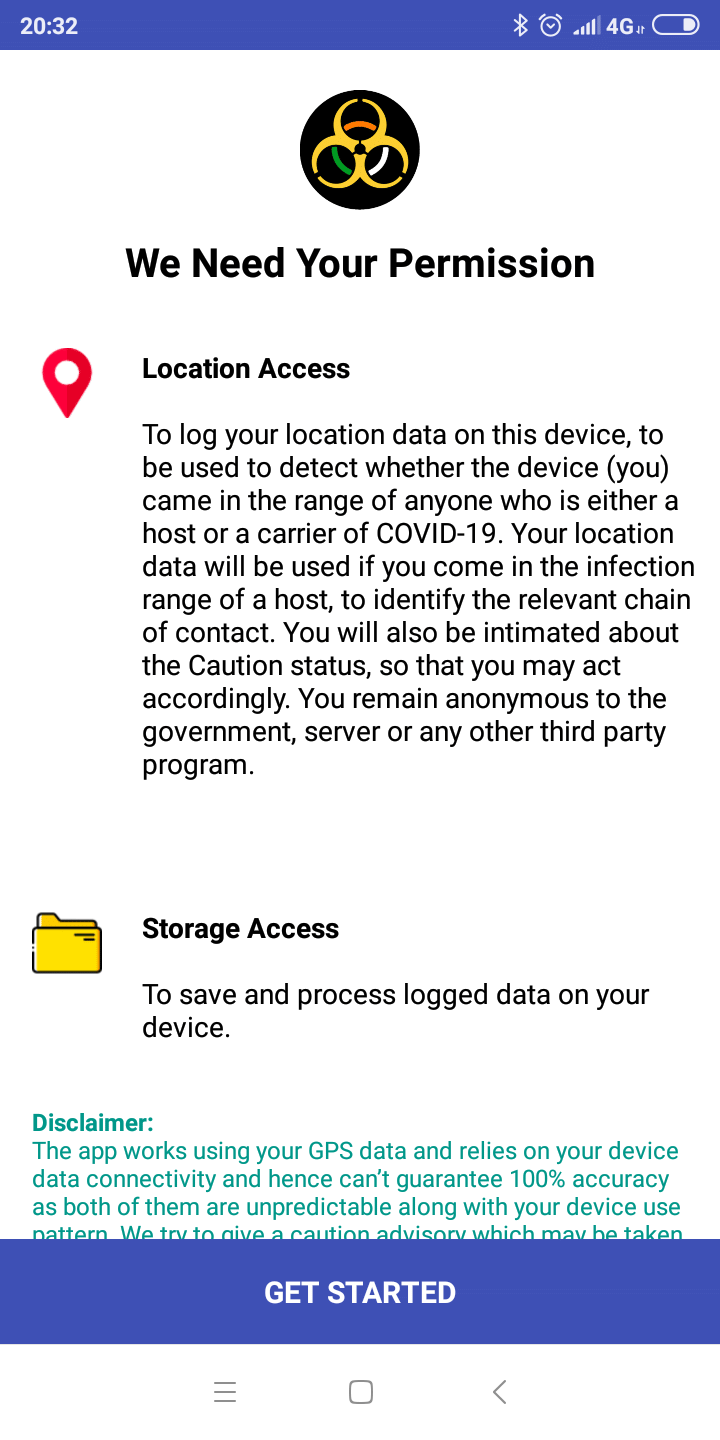
The app seeks to assure users that there’s no privacy invasion. “You remain anonymous to the government, server or any other third party program,” it states, and also outlines a disclaimer.
“The app works using your GPS data and relies on your device data connectivity and hence can’t guarantee 100% accuracy…”
The version of the app pulled down from Google Play store also had a potential vulnerability.
A user with enough technical know-how could key in anybody’s phone number and gain access to their account on the app, said Kothapalli.
To illustrate this, Kothapalli entered this reporter’s phone number to start using the app. While this reporter received an OTP via SMS to gain access, Kothapalli managed to catch hold of the password too, using a software that can intercept messages between the app and its server.
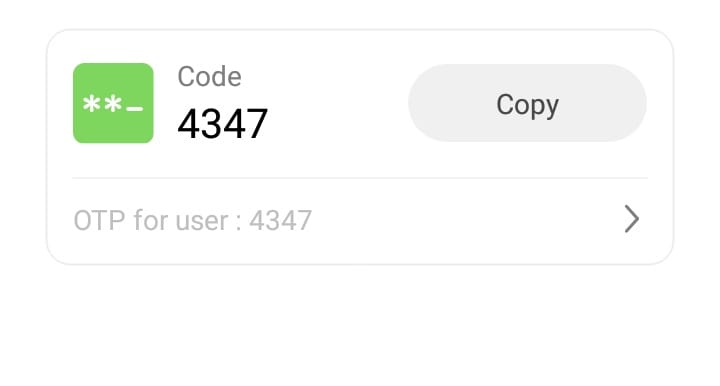
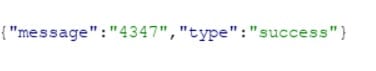
Secure apps typically don’t mention OTPs in the backend messages shared between the app and the server of its developer while the OTP verification is taking place. This prevents any attacker from intercepting these backend messages and finding out passwords.
Even so, Kothapalli noted that the vulnerability would not have any impact at present because the app did not host any personal details.
Also Read: Missing your friends? Here’s the app that can help you during lockdown





