New Delhi: Rajasthan Intelligence and Air Force Intelligence recently dismantled a cross-country espionage network with the arrest of a civilian employee stationed at Chabua Air Force Base in Assam. The accused, Sumit Kumar, 36, was allegedly leaking sensitive military data, including the locations of fighter jets and missile systems to Pakistan-based handlers for money.
Sumit’s case isn’t the only one of its kind. Whether it be the promise of quick money or the calculated lure of a honey trap, or even the slow radicalisation of a university student—India faces a homegrown—and growing—challenge to its national security. Spying is no longer about agents, but has moved to smartphones and social media. A single Instagram DM or an encrypted chat on Discord can turn a citizen into an enemy of the state.
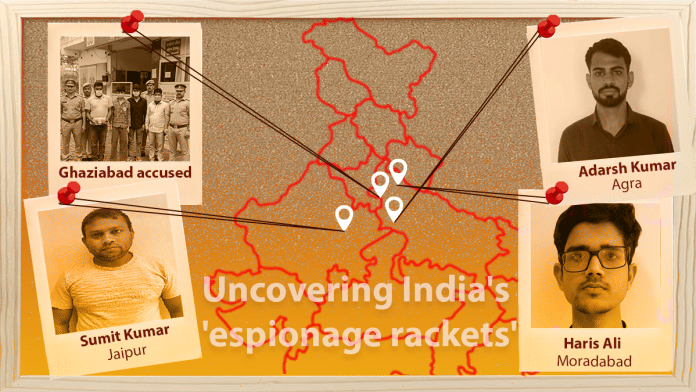
The recent flurry of arrests across Uttar Pradesh, Rajasthan, Assam—19 arrests in the last two months—have revealed how foreign-based handlers gather information. On Tuesday, the Ghaziabad Police arrested Sameer alias Shooter, 20, Sameer, 22, and Shivraj, 18 in connection with an ongoing spy case investigation.
These operations are being prosecuted under the stringent Official Secrets Act. Security agencies have found that the technology used for data transmission—either Virtual Private Networks (VPNs) to standalone, solar-powered Closed-Circuit TVs (CCTVs) has become more sophisticated, but the human element remains rooted in age-old vulnerabilities: money, honey-trapping and ideological indoctrination.
As specialised anti-terror units of state police forces continue to crack down on multiple layers of these modules, ThePrint takes a close look at the key espionage cases in March 2026 where arrests have exposed the depth of cross-border networks.
Also Read: India’s much-maligned intelligence agencies are our only hope against terror attacks
Air Force staffer in the net
Sumit, the Chabua Air Force Base accused, was found transmitting sensitive information related to the Indian Air Force to Pakistani handlers. Prafulla Kumar, Additional Director General of Police (Intelligence), said that the entire case came up in January 2026 with the arrest of Jhabararam, a resident of Jaisalmer.
During his interrogation and the subsequent investigation, the name of another suspect—Sumit Kumar—surfaced; he was found to be in constant contact with Pakistani intelligence agencies. The investigation revealed that the accused, Sumit Kumar, a resident of Prayagraj, Uttar Pradesh—was currently employed as an MTS (Multi-Tasking Staff) at the Chabua Air Force Station in Dibrugarh, Assam, police said.
“Abusing his official position, he would gather confidential information related to the Air Force Station and transmit it to Pakistani handlers via social media,” said the police.
During a joint interrogation conducted by various intelligence agencies, “it was revealed that the accused had been in contact with a Pakistani intelligence agency since 2023 and was sharing sensitive information in exchange for monetary payments,” the police said.
The interrogation further revealed that the accused had shared critical information pertaining not only to the Chabua Air Force Station but also to other military bases, including the Nal Air Force Station in Bikaner district. This information included details regarding the location of fighter aircraft, missile systems and confidential data concerning officers and personnel.
Recruiting technically proficient but poor youth
From 14 March, the Ghaziabad Police has been working on a tip-off that a group of people had been putting up CCTV cameras. When police investigated the matter, they found the group was led by two-three handlers — Naushad Ali and Suhail Malik— and the gang targeted “technically proficient” but poor youth, mostly mobile mechanics and CCTV operators, via Instagram.
The recruits filmed railway stations and security bases using GPS-tagged camera apps. The investigation also revealed the group installed solar powered CCTV coverage at Delhi Cantt and Sonepat station to provide real-time feeds to foreign numbers. The SIT held over 18 people, including six juveniles and women who were hired to avoid suspicion. While more arrests are underway, Ghaziabad Police says it has dismantled the two-year-old espionage network.
Alleged indoctrination from Moradabad
On March 16, the Uttar Pradesh Anti-Terrorist Squad (ATS) arrested Haris Ali, a 19-year-old second year dentistry student, from Moradabad. Ali, the police alleged, was operating a sophisticated online cell for the Islamic State (ISIS), using VPNs and encrypted apps like Session and Discord to spread propaganda.
Beyond recruitment, Haris also formed the Al-Ittihad Media Foundation to glorify slain terrorists and incite suicide attacks against the state. The police said his network spanned handlers in India and Pakistan, aiming to indoctrinate ‘mujahids (fighters)’ to overthrow the democratic system. Ali, a resident of Saharanpur, has been arrested under UAPA.
Classic case of honey trapping from Agra
On 10 March, the Uttar Pradesh ATS arrested 24-year-old Adarsh Kumar, alias Lucky, a Leading Mechanic in the Indian Navy, a rank equivalent to the Army’s Lance Naik—posted at Southern Naval Command, Kochi, from Chitpur Village in Agra. Adarsh, the police say, allegedly fell for a classic honey trap after connecting with a Pakistani Inter-Services Intelligence-linked profile on Instagram.
The investigation revealed that Adarsh not only shared photographs and videography of strategically important warships, but money transactions were also involved. The transition from a serviceman to an accused in an espionage case began with a simple DM on Instagram and culminated in arrest and judicial remand.
(Edited by Nardeep Singh Dahiya)